Technical description of the platform
Cryptography¶
The Waves Enterprise platform uses the Waves cryptographic algorithm.
The table below lists the cryptographic functions used.
Functionality |
Cryptographic functions and algorithms |
|---|---|
Hash coding |
Blake2b256 and Keccak256 functions consequently |
Digital signature |
Based on the Curve25519 elliptic curve (ED25519 with X25519 keys) |
Data encryption |
AES symmetric data encryption |
Confidential data encryption |
TLS v1.2 with cryptoset TLS_RSA_WITH_AES_256_CBC_SHA |
Hash coding¶
As indicated in the table above, in the Waves cryptography hash coding is performed consequently by the Blake2b256 and Keccak256 functions.
The size of an output data block is 256 bits.
Electronic signature¶
As shown in the table above, in Waves cryptography, the algorithms for key generation, and digital signatures forming and verifying are implemented on the basis of the Curve25519 elliptic curve (ED25519 with X25519 keys).
Learn more about the digital signatures generation and verification with the use of the gRPC and REST API methods in the following sections: gRPC: generation and checking of data digital signatures и REST API: generation and checking of data digital signatures.
Protecting confidential data¶
On the Waves Enterprise platform you can use the TLS protocol to protect data transmitted between nodes. The supported protocols are listed in the table above.
To enable TLS, set the node.network.tls parameter to true in the node.conf node configuration file.
If the TLS protocol is not used to create connections between nodes (the node.network.tls parameter is set to false), a TLS-like end-to-end encryption scheme using session keys based on the Diffie-Hellman protocol is used to protect transmitted confidential data (privacy). This protection will only be applied to confidential data when transmitted between nodes peer-to-peer, i.e. between two network members.
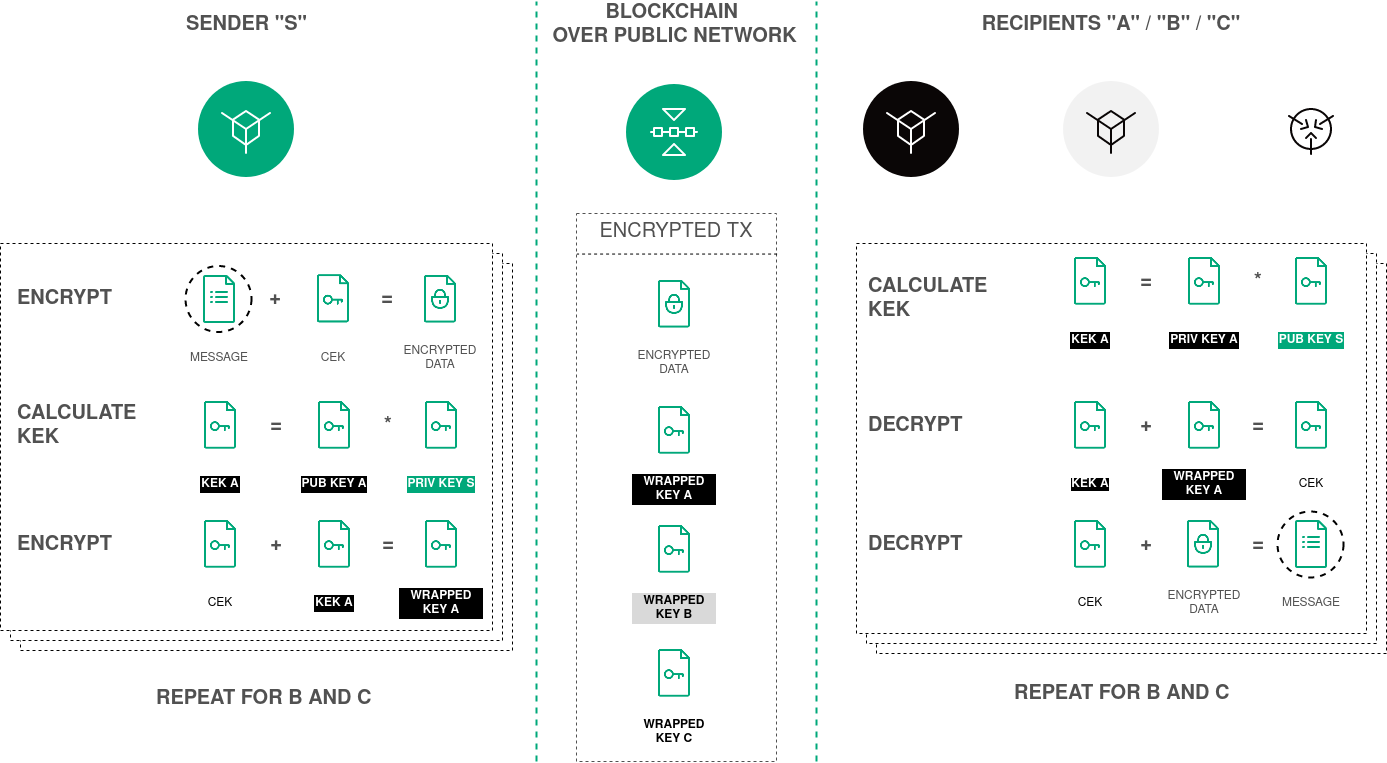
Here you can see the scheme of the text data encryption procedure based on the Diffie-Hellman protocol:
Note
The platform also uses theTLS protocol when working with smart contracts for the following connections:
connection with the Docker-host (Docker-TLS);
connection from a smart contract to a node via gRPC and REST API.
TLS setup and usage in these cases are documented in the General platform configuration: execution of smart contracts section.